In previous post I explain about the different groups we can create in a domain environment. In an organization some time you may need to grant permissions for different users to manage these groups and its memberships. But some time it is better if we can lock some of these memberships for security reasons. For example let’s assume you have a group which have access to financial records of the organization which should only have access to upper management. So membership of the group is important.
Restricted group policy is the answer for that. Using group policy you can specify the membership and enforce. So no one can add or remove members.
Let’s see how we can do it in domain environment.
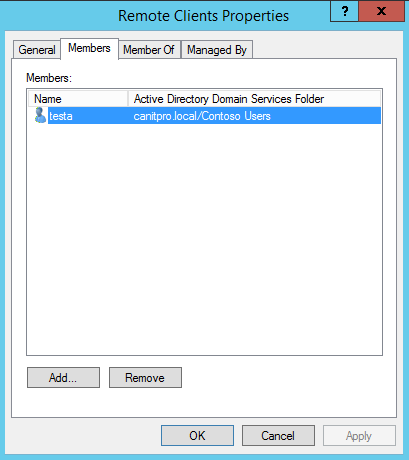
For the demo I created a group called “Remote Clients” and made usera and userb members of it.
But for the demo I need to restrict the group membership and only use testa user as a member.
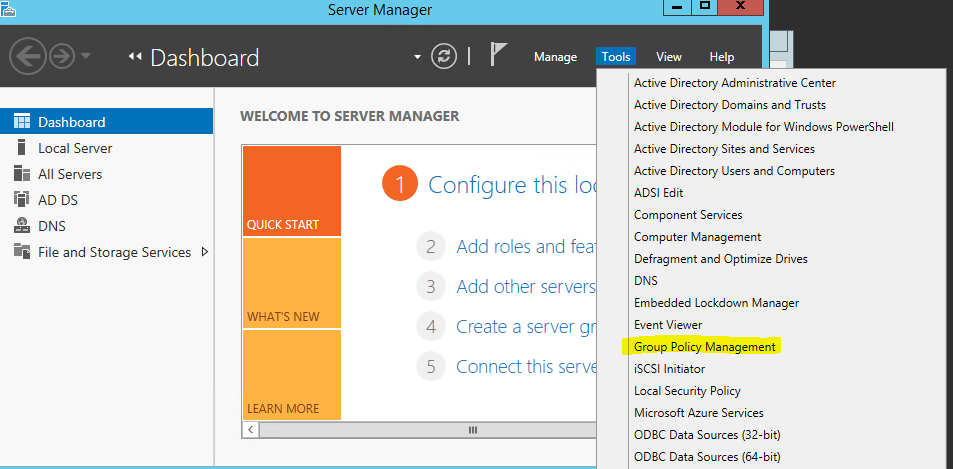
To do it go to server manager > tools > group policy management
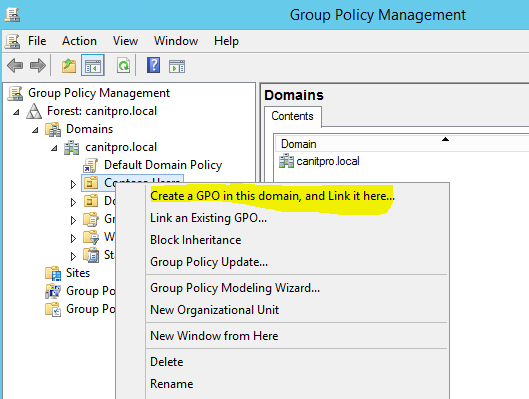
Then go to the OU you wish to apply restrict group policy. If it’s going to apply for the organization you can make it global policy as well. Then right click on OU name and select “Create GPO in this domain an link it here”
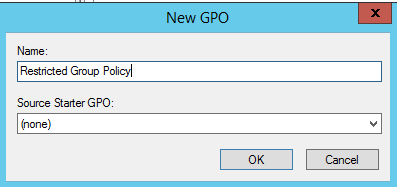
Then provide the name for new policy and click ok.
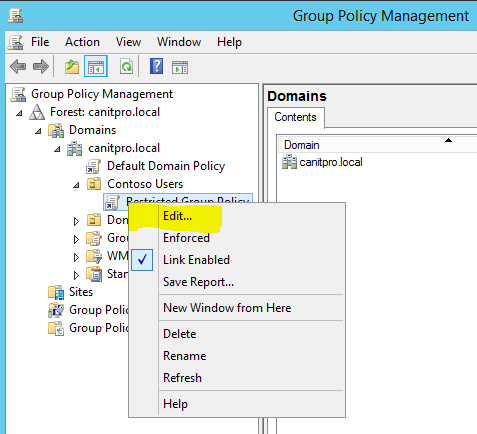
Then go to the OU again and right click on the new GPO and click on edit.
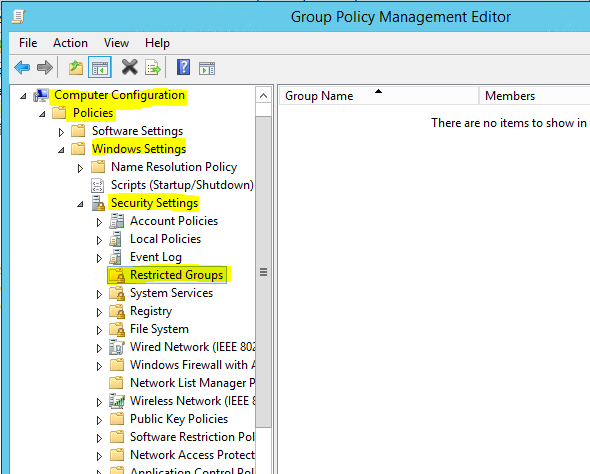
Then go to Computer Configuration\Policies\Windows Settings\Security Settings\Restricted Groups folder
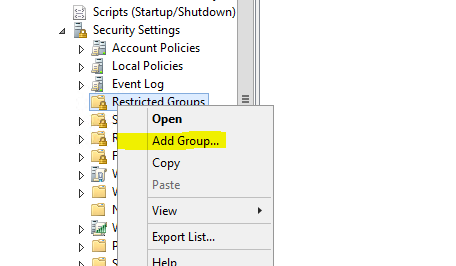
Right click on it and click “Add Group”
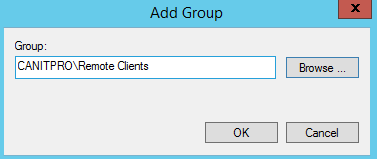
Then go and select the group you need to add, in my demo its Remote Clients. Then click ok.
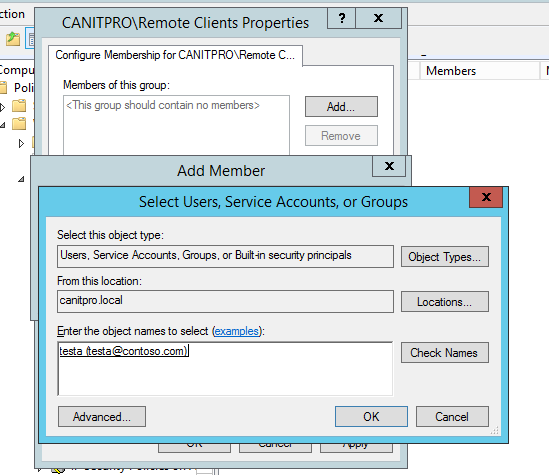
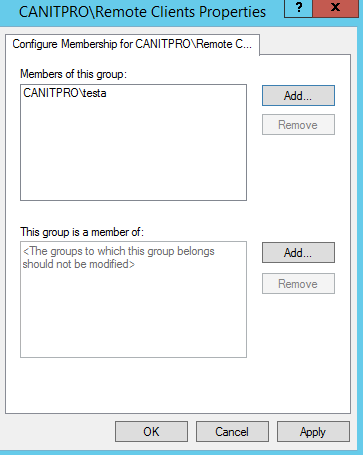
Then it gives option to add members to the group. Also if this group should need to be added as member of another group.
In here I added user testa and I need to force the membership only to this user.
Now it’s all done. Next time when policy applied it will overwrite the current membership.
If you have any question feel free to contact me on rebeladm@live.com